How it Works
ZCAM verifies photo authenticity via a combination of hardware-backed attestation, cryptographic signatures, and optional zero-knowledge proofs.
When a user takes a photo, ZCAM signs it using an Apple attested, secure enclave key. This attestation is embedded into the photo using the C2PA standard. Optionally, the attestation can be wrapped in a zero-knowledge proof for enhanced privacy.
The system works in three steps:
-
Capture: Take a photo and sign it with a hardware-backed key, attaching a verifiable attestation to the photo.
-
Prove (optional): Generate a zero-knowledge proof of the capture attestation.
-
Verify: Validate the photo's authenticity using either bindings or ZK proof verification. Bindings verification verifies the Apple App Attest signature directly. It's faster and can be generated offline. ZK proof verification generates a zero-knowledge proof for enhanced privacy, but requires network access for proof generation.
Components
The SDK is built on three core technologies:
- Apple's App Attest guarantees that signing keys are generated and stored in the iPhone's secure enclave, tied to a specific app.
- C2PA embeds verifiable provenance metadata, including capture details and edit history, directly into the image file.
- SP1 zero-knowledge proofs optionally wrap verification into succinct, easily verifiable proofs using Succinct's SP1 zkVM.
Apple App Attest and Secure Enclave
ZCAM uses the Secure Enclave to store signing keys and Apple's App Attest service to ensure that a photo was signed by the ZCAM SDK.
App Attest is designed to let backend services verify that requests are coming from a legitimate app. It works by generating a signing keypair in the device's secure enclave that only the specific app can access. Apple then attests that the keypair was generated on that app and that the app itself has not been tamepred such that any subsequent signatures are guaranteed to originate from it.
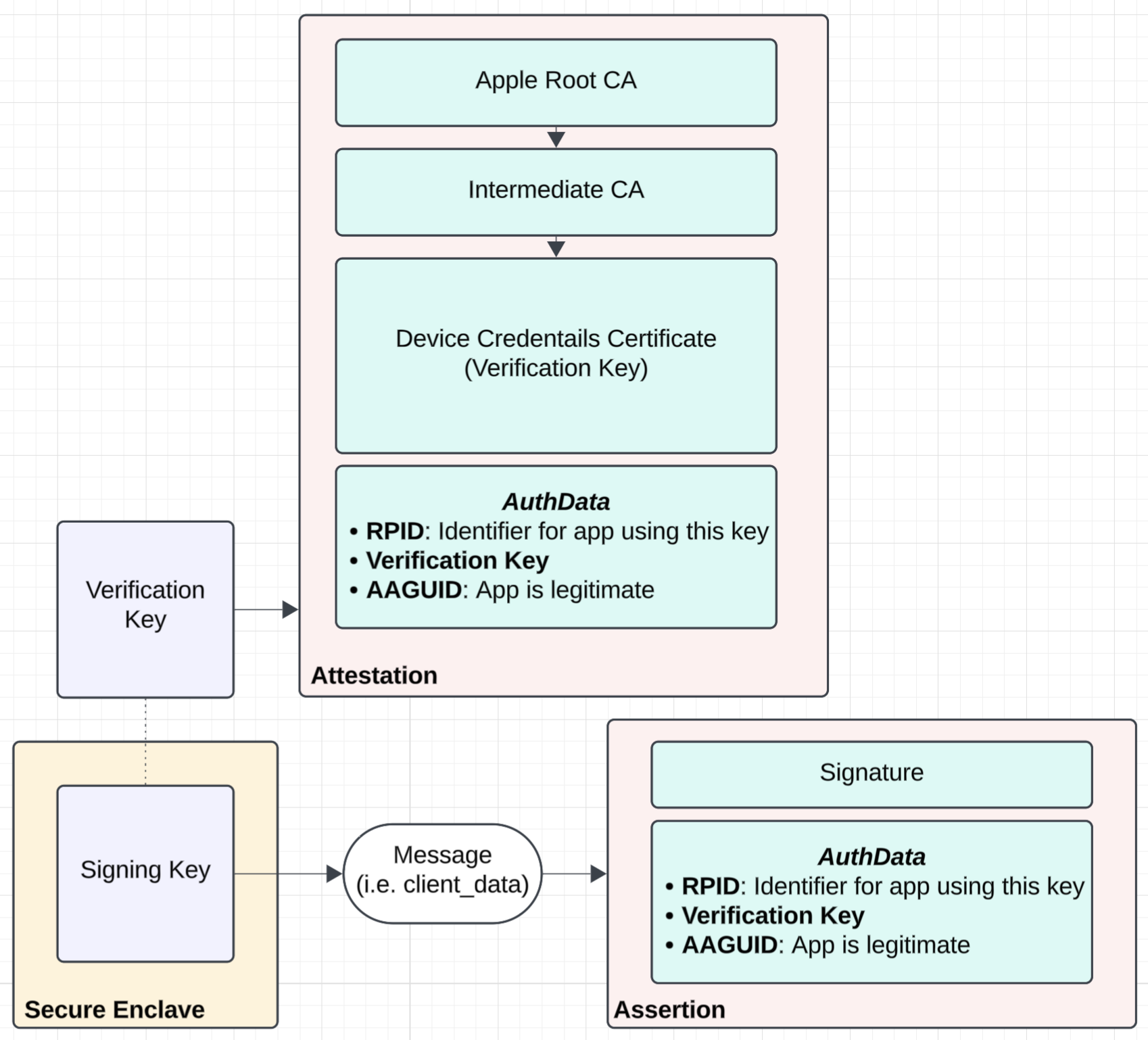
The App Attest protocol provides an attestation from Apple's servers, bound to a unique nonce and the public key of the secure enclave keypair. The app attaches this attestation to requests so the receiving service can verify authenticity.
ZCAM uses App Attest differently in two ways:
- The nonce is unique per photo and is derived on the device itself, rather than received from a backend service.
- The attestation can be verified directly (bindings verification) or inside a zero-knowledge proof (ZK verification), rather than by a backend service.
The Secure Enclave is a coprocessor in Apple devices that provides an isolated environment for cryptographic operations. Keys stored in the Secure Enclave cannot be extracted or copied, are protected even if the device is compromised, and can only be used by the app that created them. ZCAM stores both the device key (for signing photo hashes) and the content key (for signing C2PA manifests) in the Secure Enclave. This ensures that even if an attacker gains device access, they cannot forge signatures using the ZCAM signing key.
C2PA
ZCAM uses C2PA to embed attestation data (and optionally zero-knowledge proofs), proving that the photo was taken on an iPhone and signed using a secure enclave key that only the ZCAM SDK can access.
See the C2PA page for in-depth information on C2PA and how ZCAM uses C2PA.
SP1 Zero-Knowledge Proofs
Zero-knowledge proofs let one party prove to another that a statement is true without revealing anything beyond the statement's validity.
ZCAM uses SP1, Succinct's zero-knowledge virtual machine (zkVM). SP1 proves the correct execution of programs compiled for the RISC-V architecture, meaning it can run and prove programs written in Rust, C++, C, or any language that compiles to RISC-V.
SP1 offers three key benefits:
- Maintainability: Write ZK programs in standard Rust without custom DSLs or complex circuits
- Faster Development: Skip months of low-level ZK engineering
- Performance: State-of-the-art proving speed and efficiency, benchmarked in production
In ZCAM, SP1 generates proofs that verify the photo was signed with a valid Apple App Attest key, the signature matches the photo hash, and the attestation chain is valid. These proofs are small, fast to verify, and don't reveal the underlying attestation data.
As mentioned above, zero knowledge proofs are optional. You can use ZCAM with bindings verification alone. ZK proofs add privacy guarantees but require internet access to request proofs from the Succinct Prover Network. There is also higher latency given the time required for the network to prove the verification of an attestation.